SAP GUI vulnerabilities are a critical part of SAP security and they should not be overlooked during SAP security audits and regular SAP scans.
SAP GUI security affects the security of workstations that SAP users are using for connecting to their SAP systems. It can be attacked locally as well as remotely through the system using backwards connections.
We have presented the first remote attack vectors of backwards infection at the Chaos Communication Club annual congress in 2010. SAP AG was kind enough to release patches and give credits to us and the new security center in SAP GUI, the security settings, is a result of our cooperation. We are credited for the SAP Note 1483525 [New security center in SAP GUI 7.20 and later] by SAP AG.
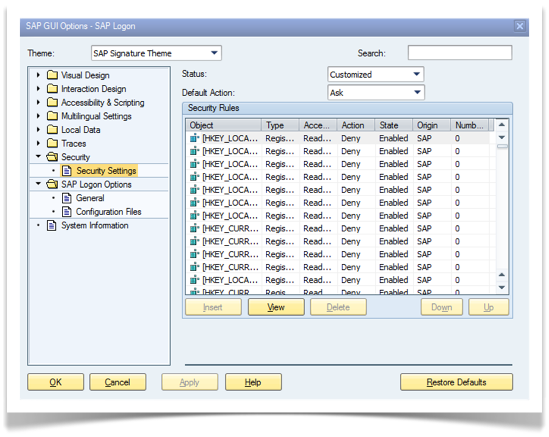
Protecting SAPGUI plays an important role in SAP security. SAP consultants and BASIS administrators connect to many SAP systems during their work day. If any of those systems would be a malicious SAP system, exploits could be run on the client side which would affect their workstation security. However, the following appears when searching for it.
Current Status of SAP GUI Security
A basic search on SAP GUI security brings the following search suggestion:
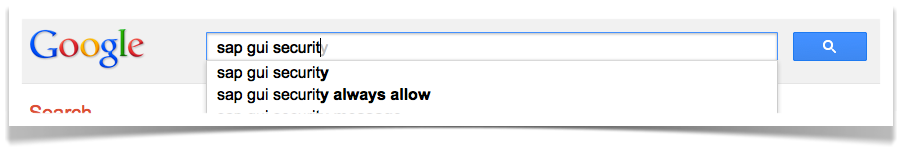
Of course it is debatable whether the ergonomics of the newly introduced security features could be improved. Nevertheless, we strongly recommend avoiding having “always allow” for all of the actions and keeping SAP GUI always with the latest security patches. Details below.
Why SAP GUI Security is important
At any enterprise, there are SAP systems such as test systems where security is less a concern compared to other systems. A typical sap consultant connects to many SAP systems. For external consultants, this means foreign SAP systems. Also in many companies, SAP BASIS administrators use remote training systems for learning new features. These training systems can be subscribed for a very low charge.
Hacking the SAP System – Initial Compromise
If any such “low security” SAP system or a foreign SAP system gets compromised, the security impact might seem to be big initially. Please look at the following scenario:
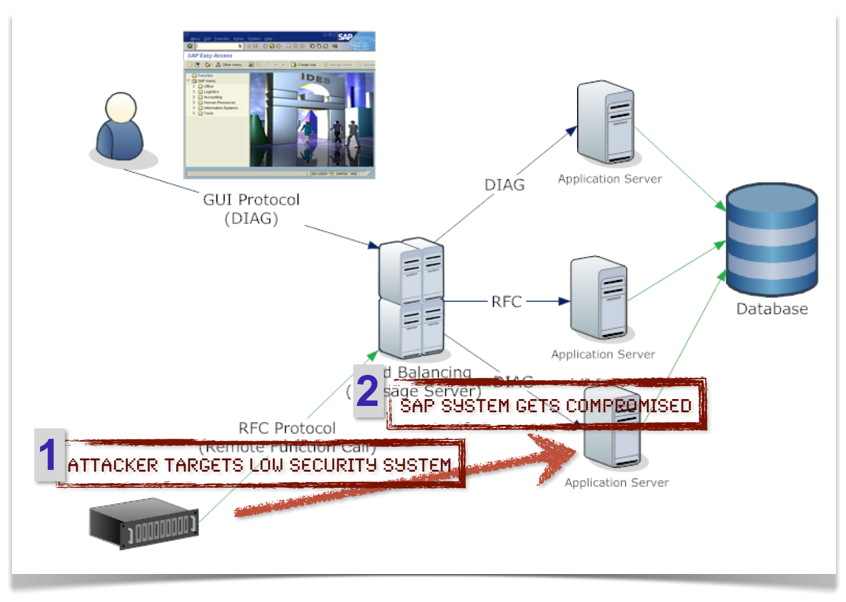
One system is compromised. Either since it had default passwords, it contained many publicly available SAP security issues, or the attacker simply had powerful rights with it. We assume the attacker now has rights to manipulate it.
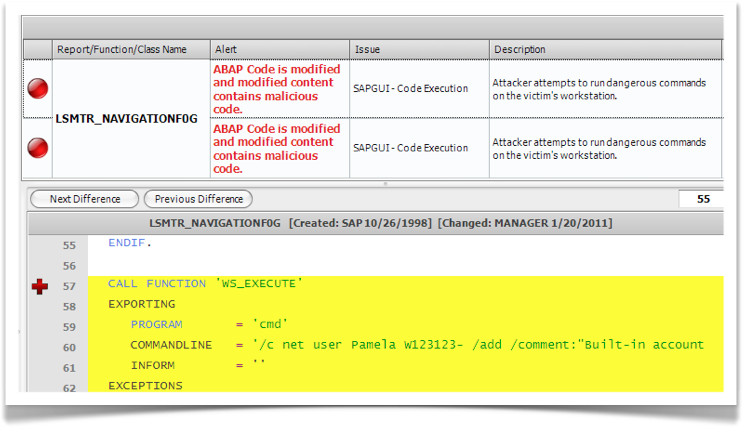
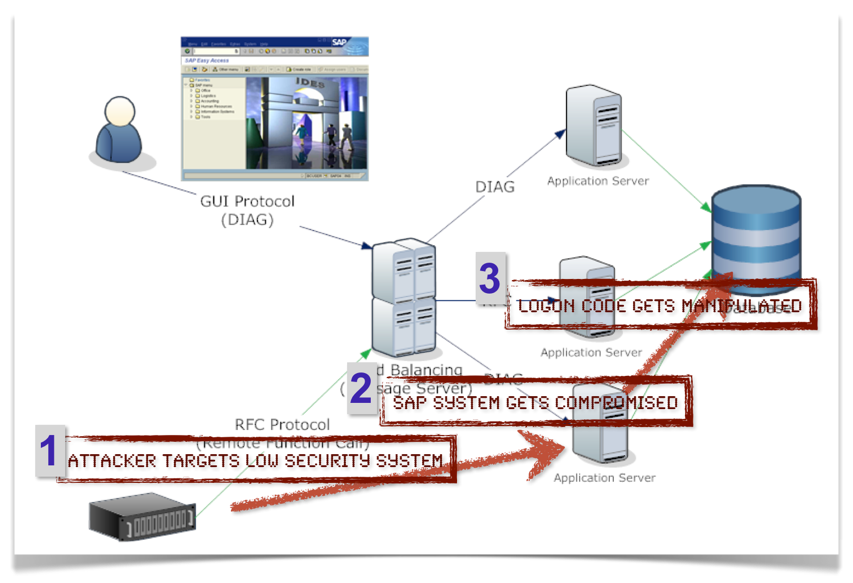
Manipulating the ABAP code repository
As you might already know, it is possible to manipulate SAP’s default ABAP programs.
In the following picture, the ABAP repository is manipulated and the attack is ready to be launched. We can call it a logic bomb.
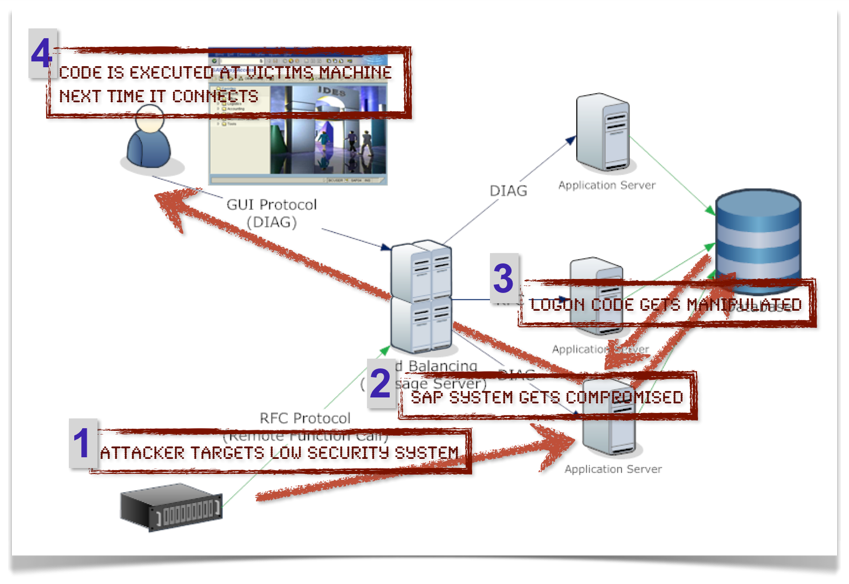
Planting the Payload – Exploiting SAP GUI functionality
SAP GUI security becomes important at this part. At this moment, the affect of the bomb is solely at the imagination and hands of the attacker. You might already know that SAPGUI allows many actions to be run on the presentation server (SAP GUI). These actions are
-
Executing operating system commands
-
Reading from files
-
Writing to files
-
Reading registry keys
-
Writing registry keys
and more.
Attacking SAP GUI clients and SAP users
When an SAP user connects to the system, the commands that the attacker has planted will be executed on the victims machine without any notification. Now on the newest SAP GUI versions, it generates a prompt.
Conclusion
As mentioned in a recent SAP ransomware article, you can connect to a malicious SAP system randomly by accessing a server you regularly access or by clicking a SAP logon shortcut which takes you there. So, best is keeping your SAP GUI secure with latest patches, avoiding enabling “Allow All”, and always reviewing the prompt when it appears.
How ESNC can help
ESNC offers three approaches for addressing issues similar to this:
SAP Security Assessments
ESNC SAP security assessments allow discovering vulnerabilities in the client applications.
Realtime SAP security monitoring and attack detection
Enterprise Threat Monitor detects attacks to your systems
Detecting Malicious Code on SAP System
ESNC Security Suite code security module allows detecting backdoors and malicious code changes in SAP code.