We support you by on-site SAP security reviews, where we focus both on insider threats and Internet based attack vectors. Based on the SAP security audit results; performance, and availability problems can be prevented before they affect critical operations.
We provide technical assessment of your SAP infrastructure to help prevent the problems that can affect your operations or daily business. Technical SAP assessments combined with SAP penetration testing help uncovering most critical SAP security issues and raising security awareness in SAP domain.
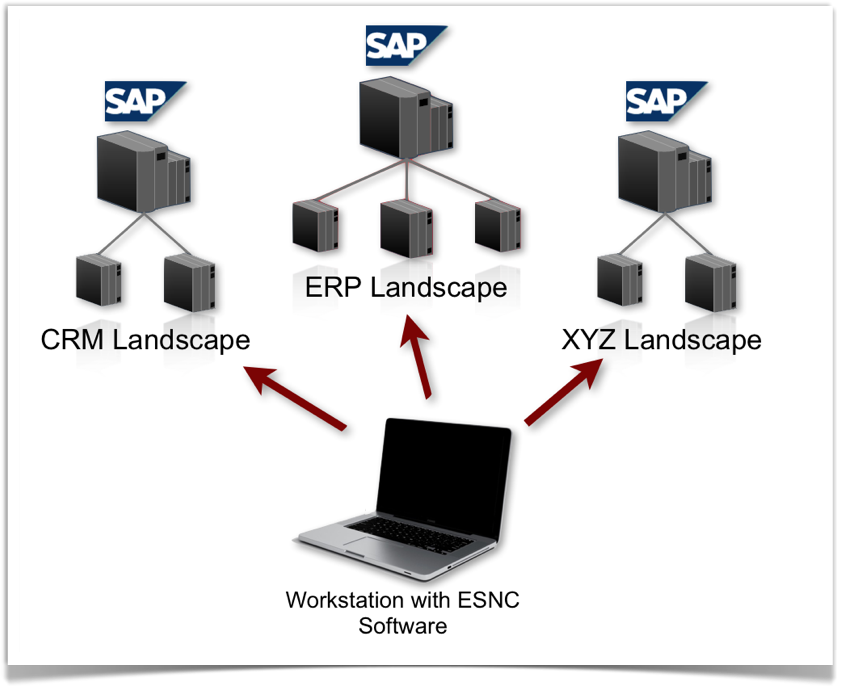
By utilizing ESNC software during SAP security audits via SaaS (software as a service), we are able to deliver very high quality SAP security scan results using minor manual effort. During our SAP assessments, either we bring our secure audit workstation on-site or use an existing workstation in customer premises as SAP analysis center.
On-site SAP Security Review – Scope
We conduct the SAP security check on critical components of your SAP systems such as (but not limited to):
-
SAP Gateway Configuration
-
SAP Message Server Configuration
-
Authentication
-
SAP User Password Policy
-
SAP User Authorizations
-
SAP Web services, ITS security
-
Enterprise Portal Security
-
SAP System Patches
-
OS/Database Security
-
SAP Router Security
-
SAP Security Auditing
Based on the SAP security assessment, we provide an SAP security audit report, which includes the discovered issues and suggestions for fixing them. After the SAP security audit, we help you in hardening your security infrastructure, mitigating configuration related SAP security vulnerabilities, developing SAP security guidelines and testing the effectivity of the applied changes.
Our reporting system is adjustable your needs for continuous SAP assessments. We deliver periodic SAP security reports to you, depending how often you want and with data that reflects your system completely. This information can be used in management dashboards for making the progress in SAP security actions more visible.
Per request, we do SAP vulnerability assessments or conduct SAP security configuration reviews on more focused areas such as: